A team at the University of Luxembourg’s (SnT) is working with to improve the security of smart contracts. SnT offers expertise in this area, in which there is a “lack of activity, skills and knowledge in Luxembourg,” said , Head of the Service and Data Management () research group at SnT.
Their work with Spuerkeess is part of SnT’s , through which it collaborates with some 50 members from within industry and the public sector on strategic ICT areas of concern. This particular project is co-funded by SnT and Spuerkeess, and has received external funding from the (FNR).
Blockchain-enabled programs
Smart contracts are essentially computer programs running on a blockchain.
A blockchain is a digital ledger of transactions that is duplicated and distributed across a network of computers. When set up correctly, this way of recording information makes it hard or impossible to change, hack, or cheat the system. However, if there are errors in the initial set-up of smart contracts, this can make the system vulnerable to attacks, as they cannot be modified and are already a high-interest target for criminals.
Major research partner
Spuerkeess is one of SnT’s major research partners. “We now have three Ph.D. students and three research associates working with Spuerkeess,” explained State.
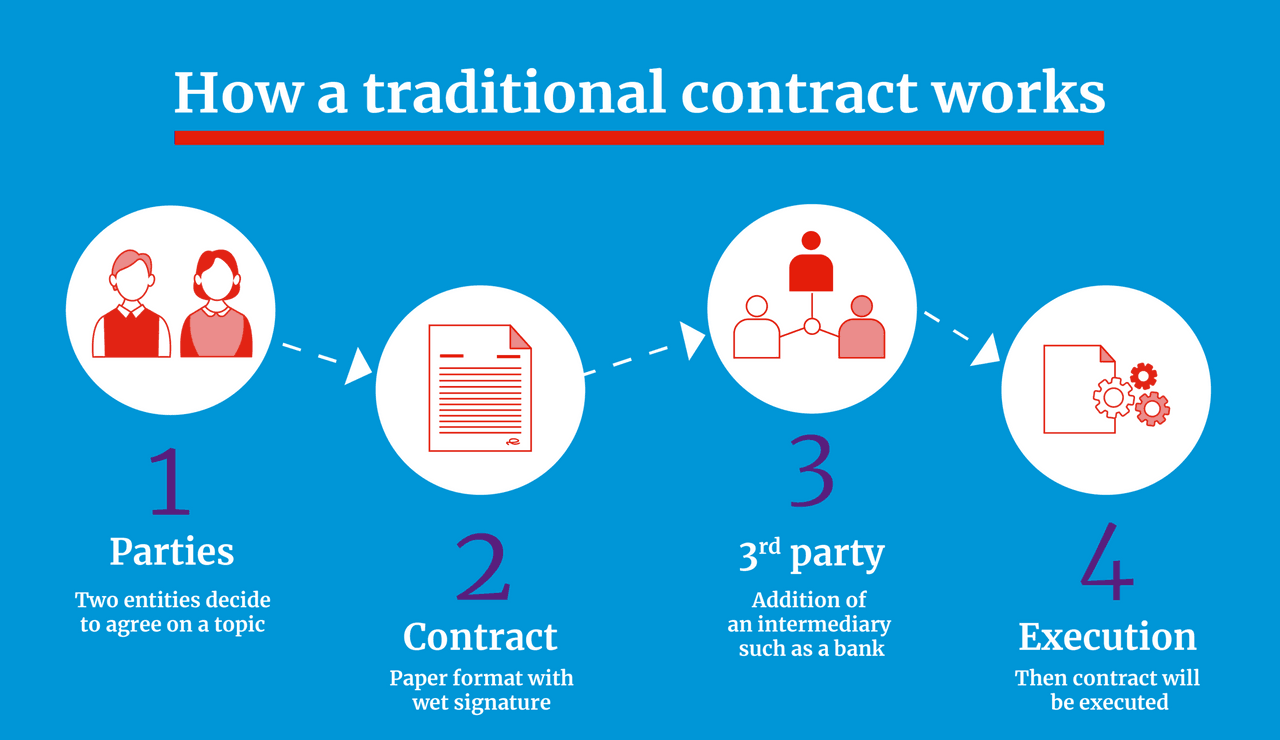
How a Traditional contract works (Illustration : Maison Moderne)
The project’s aim is to help Spuerkeess understand the risks of smart contracts and mitigate them in any future application. State pointed out that smart contracts are a very new area. “There is a lack of tools and approaches to find and repair vulnerable smart contracts,” said State. Torres is working on a way to automate this process, to detect and patch up holes before hackers can find them.
Money in the system
Torres explained that one of the advantages of smart contracts is that they can include code that manipulates the transfer of funds. “Right away you have a built-in capability to transfer funds across accounts, which in normal software you don’t have out of the box”, he said. This creates a security risk if there’s a vulnerability that goes undetected within the code.
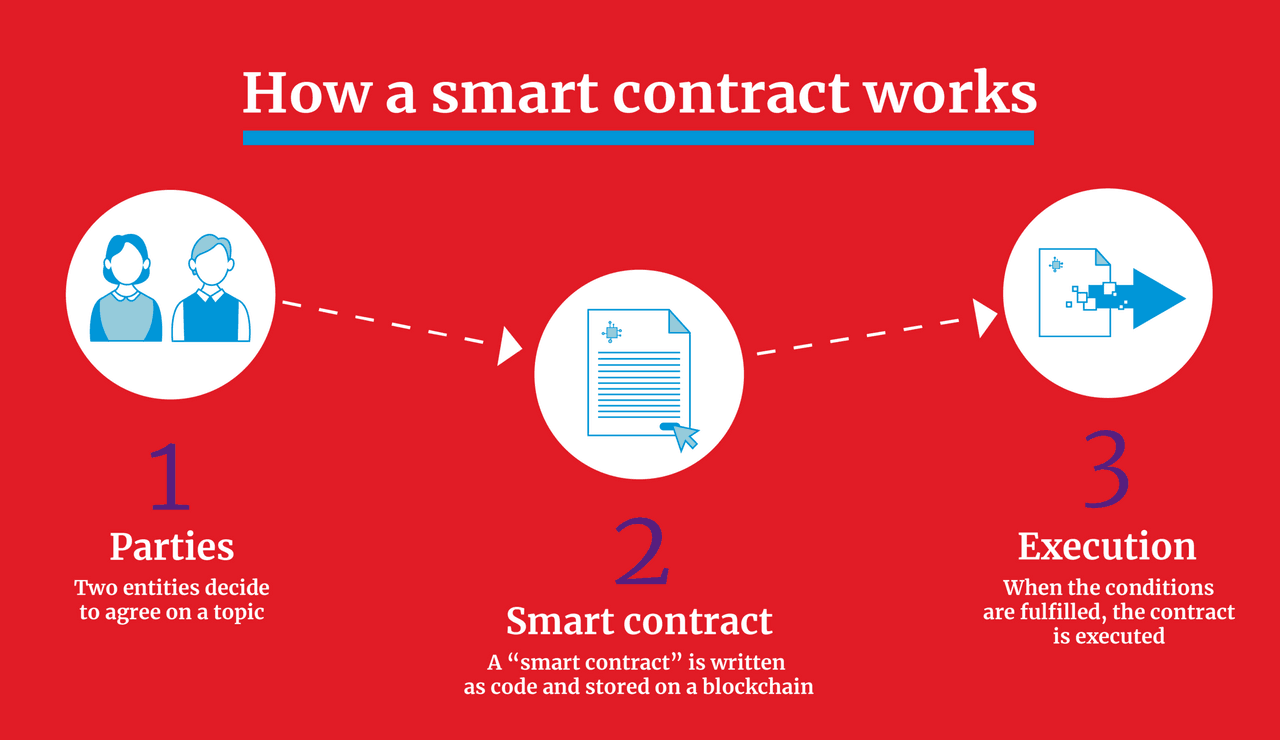
How a Smart contract works (Illustration : Maison Moderne
The financial losses from theft in smart contract history in the US alone are staggering, with some high-profile cases amounting to anywhere from $50-100+ million US over the last few years. These include the DAO hack of 2016 and the Parity hacks of 2017, State explained. In fact, researchers in 2017 that $500 million US was lost or stolen because of poorly coded contracts.
Publicly accessible
Another distinction for smart contracts is that they are publicly accessible.
Everybody can send a transaction to a smart contract, which is very different from the normal security paradigm in which your infrastructure is protected by firewalls.
He also explained that smart contracts are supposed to be accessible to all participants of a specific blockchain. Unfortunately, he explained, “it means that a participant with a criminal intent can just as easily interact with a smart contract as a legitimate person.”
Managing the risk
Torres recommended that companies “shouldn’t be afraid of using smart contracts because of their security concerns.” He explained that it would be better to proactively improve security by educating developers to use secure practices and various tools that check the security of their code.
One of the key ways to secure smart contracts, explained State, is contracting external firms to audit your code. “Some are using tools that we have developed and that we have released open source (under an MIT license),” he explained.


